Alternatives to Threat Watch
Explore the best alternatives and competitors to Threat Watch.
Explore 18 alternatives to Threat Watch. Compare features, pricing, and find the best fit for your needs.
Decker
Decker empowers consultants to create, collaborate, and monetize deliverables with AI-driven workflows and expert support.

FX Radar
FX Radar delivers real-time forex news in seconds with AI-powered analysis and a professional trading journal for comprehensive performance tracking.

AI Business Name Generator
Discover the perfect brand identity instantly with our AI Business Name Generator, creating unique, catchy, and brandable names for startups.
Roipad
Roipad delivers data-driven insights to refine your B2B SaaS positioning, ensuring your GTM strategy targets the right market for success.

MarketWrk
MarketWrk automates CPG pricing, MAP compliance, and review monitoring, transforming data into actionable insights for your team.

Opal44
Opal44 delivers AI-driven insights from your website traffic in clear, simple language, making analytics easy to.

Fusedash
Fusedash transforms raw data into clear dashboards and charts for instant team insights and action.
finban
Finban is your liquidity operating system, providing clear cash forecasts and scenarios for confident financial.

Zignt
Zignt automates contract workflows for quick, secure, and legally binding e-signatures without per-signature fees.

aVenture
aVenture is an AI-driven platform that delivers in-depth startup research and venture capital insights for informed.

iGPT
iGPT transforms messy email data into trusted, context-aware answers for enterprise workflows and AI agents.

Karolium
Karolium is a zero-code platform that empowers enterprises to rapidly create and customize AI-driven business solutions.

Promotron
PromoTron revolutionizes the promotional products industry with cloud-based solutions for streamlined e-commerce and.

Pursuit
Pursuit helps businesses identify and engage public sector opportunities before RFPs, maximizing revenue potential.
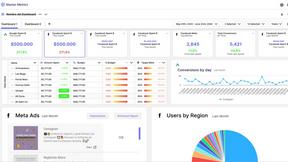
Master Metrics
Master Metrics empowers agencies to enhance marketing performance through AI-driven data analysis and smart dashboards.

CMMC ROI
CMMC ROI helps you calculate compliance costs and potential returns to secure lucrative DoD contracts with confidence.
Deeploy
Deeploy provides organizations with robust AI governance for risk management, compliance, and scalable oversight of AI.
About Threat Watch Alternatives
Threat Watch is a unified cybersecurity intelligence platform, operating within the business intelligence and security analytics category. It delivers a comprehensive, real-time evaluation of an organization's external digital health by aggregating data from diverse sources like the dark web and breach databases, transforming it into prioritized, actionable insights for proactive defense. Users often explore alternatives for various practical reasons. These can include budget constraints and specific pricing models, the need for integration with an existing security stack, or a requirement for different feature sets tailored to unique organizational workflows. The search for a different solution is a natural part of finding the optimal fit for a company's size, maturity, and specific risk profile. When evaluating any alternative, key considerations should include the depth and real-time nature of threat intelligence coverage, the clarity and actionability of the presented insights, and the platform's ability to automate monitoring to reduce manual overhead. The ideal solution should not just collect data, but effectively contextualize it to empower strategic, risk-based decision-making across technical and business teams.
FAQs about Threat Watch Alternatives
What is Threat Watch?
Threat Watch is a comprehensive cybersecurity intelligence platform that provides a real-time, unified evaluation of an organization's external security posture by analyzing digital assets, vulnerabilities, and exposures from sources like the dark web and breach databases.
Who is Threat Watch for?
It is designed for IT security teams, risk management professionals, and business leaders in organizations of all sizes who need to move from a reactive to a proactive, intelligence-driven cybersecurity strategy.
What are the main features of Threat Watch?
Its core features include a comprehensive cyber health dashboard for a holistic security view and real-time exposure detection for compromised credentials, breached assets, phishing sites, and leaked company data.
Why choose Threat Watch?
Threat Watch is chosen for its ability to transform overwhelming threat data into prioritized, understandable insights, enabling faster and more efficient threat identification and risk-based remediation.