iGPT vs Threat Watch
Side-by-side comparison to help you choose the right tool.
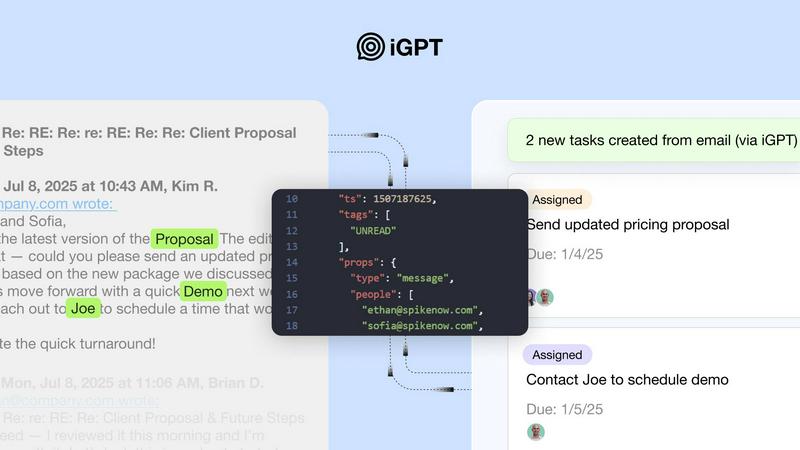
iGPT transforms messy email data into trusted, context-aware answers for enterprise workflows and AI agents.
Last updated: March 1, 2026
Threat Watch
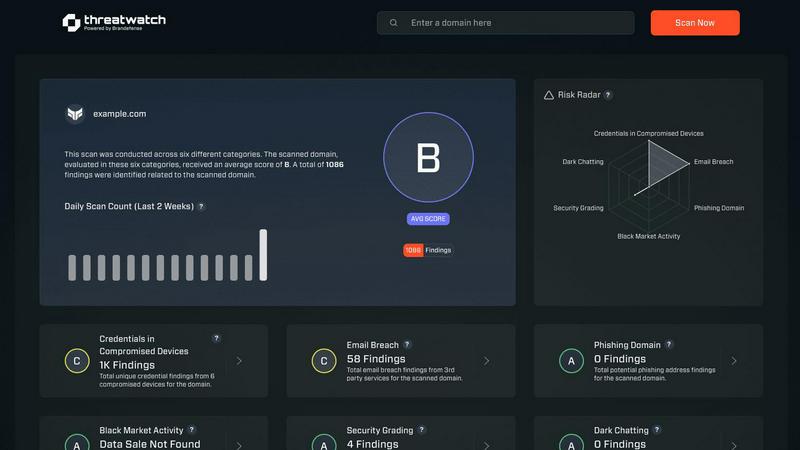
Threat Watch instantly evaluates your organization's complete cybersecurity health across all critical categories.
Last updated: March 1, 2026
Visual Comparison
iGPT
Threat Watch
Feature Comparison
iGPT
Unified Intelligence Endpoint
iGPT consolidates the entire complexity of email intelligence into one simple API call. Instead of managing separate systems for retrieval, context building, and reasoning, developers send a single natural language request. This unified endpoint handles semantic and keyword search, thread reconstruction, attachment processing, and optimal context shaping automatically, delivering a ready-to-use, structured response in seconds. This dramatically reduces development time and maintenance overhead.
Advanced Context Engineering Framework (CEF)
At the heart of iGPT is a sophisticated framework that automatically engineers the perfect context from chaotic email data. It intelligently processes and indexes messages and attachments in real-time, reconstructs full conversation threads across participants and time, and extracts text and data from documents like PDFs and spreadsheets. The system then optimizes this information for your LLM, eliminating the need for manual prompt tuning and ensuring responses are deeply contextual and accurate.
Enterprise-Grade Security & Auditability
iGPT is built with a zero-trust security model from the ground up. It guarantees zero data training, meaning your information is never used to improve models. It employs strict OAuth-based Role-Based Access Control (RBAC) for every request and operates on a zero data retention policy, processing inferences solely in memory. Furthermore, it provides a comprehensive audit trail, ensuring every answer is fully traceable back to its source messages and attachments for complete compliance.
Real-Time Ingestion & Hybrid Retrieval
The platform ensures your AI agents operate on the most current information by indexing new emails and attachments instantly as they arrive. Its retrieval system employs a powerful hybrid approach, combining semantic understanding, keyword matching, and configurable filters. These results are then intelligently scored and reranked within a single pipeline, ensuring the most relevant snippets from vast mailboxes are surfaced with high precision and speed.
Threat Watch
Comprehensive Digital Footprint Analysis
Threat Watch performs a deep and continuous scan of an organization's external digital presence, identifying all internet-facing assets, domains, and associated infrastructure. This foundational feature maps the entire attack surface, ensuring no blind spots are left unmonitored, which is critical for understanding the scope of potential vulnerabilities and exposures that could be targeted by malicious actors.
Dark Web & Breach Intelligence Monitoring
The platform actively surveils the dark web, underground forums, and a vast array of breach databases to detect if corporate credentials, sensitive data, or intellectual property are being traded or discussed. This proactive monitoring provides early warning signs of compromise long before traditional security tools might alert, allowing for preemptive action such as credential resets and security policy enforcement.
Real-Time Phishing & Impersonation Detection
Threat Watch continuously scans for phishing campaigns, fraudulent domains, and brand impersonation attempts that target the organization and its employees. By identifying malicious sites and email addresses that mimic legitimate ones, it helps prevent successful social engineering attacks and protects the organization's brand integrity and stakeholder trust.
Prioritized Risk Scoring & Actionable Insights
Beyond mere data aggregation, Threat Watch employs advanced correlation and analytics to assign contextual risk scores to every discovered threat and vulnerability. This prioritization transforms raw data into a clear, actionable roadmap for security teams, directing remediation efforts to the issues that pose the most significant business risk first, thereby optimizing resource allocation and response efficiency.
Use Cases
iGPT
AI-Powered Email Assistants
Organizations can build intelligent agents that draft, prioritize, summarize, and act on email with full historical and attachment context. These assistants can manage inboxes, highlight urgent threads, and generate draft replies based on the complete conversation history and related files, turning individual productivity tools into powerful, context-aware copilots for entire teams.
Automated Workflow & Task Management
iGPT enables the automation of routine workflow processes directly from email threads. It can automatically parse conversations to identify decisions, extract action items, assign owners, and set deadlines. It can also flag stalled discussions or pending approvals, seamlessly turning email dialogues into structured tasks in project management or CRM systems without manual intervention.
Customer Support & Success Copilots
Support and customer success teams can leverage iGPT to instantly rebuild a customer's entire story. The API can analyze long, complex email chains with multiple participants and shifting tones, alongside all attached tickets and documents, to provide support agents with a immediate, comprehensive summary of the issue, past interactions, and agreed-upon solutions, drastically reducing resolution time.
Compliance, Auditing, & CRM Intelligence
For compliance-sensitive industries, iGPT creates an immutable link between AI-generated insights and their source material. It can trace feedback, approvals, and rationale directly back to the original email and attachment, providing a clear audit trail. Similarly, sales teams can use it to extract deal momentum, key decisions, and stakeholder sentiment directly from email threads to enrich CRM records.
Threat Watch
Proactive External Risk Management
Security and risk management teams utilize Threat Watch to gain a continuous, outside-in view of their organization's security posture. This enables them to identify and assess external threats—like exposed databases, misconfigured cloud storage, or leaked credentials—before they are exploited, allowing for proactive mitigation and strengthening of the overall security framework.
Accelerated Incident Response & Investigation
During a suspected breach or security incident, Threat Watch serves as a critical intelligence source. Teams can quickly investigate if corporate assets or employee credentials have appeared in recent breach dumps or dark web markets, providing crucial context for the incident's scope and origin, which dramatically speeds up containment and eradication efforts.
Third-Party & Supply Chain Risk Assessment
Organizations can extend the platform's monitoring capabilities to assess the cybersecurity health of key vendors, partners, and suppliers. By understanding the external risks present in their supply chain, businesses can make more informed partnership decisions and enforce stronger security requirements, reducing third-party risk exposure.
Executive & Board-Level Security Reporting
Threat Watch provides clear, non-technical dashboards and reports that translate complex threat data into business-centric metrics. This empowers CISOs, executives, and board members to understand the organization's cyber risk in financial and operational terms, facilitating better-informed strategic decisions and cybersecurity investment justifications.
Overview
About iGPT
iGPT is a pioneering email intelligence API engineered to bridge the critical gap between enterprise email data and modern AI-driven workflows. In a business landscape where email remains the central nervous system for communication, collaboration, and decision-making, traditional AI systems often fail to navigate its inherent complexity—long threads, nested attachments, and fragmented conversations. iGPT solves this by providing a secure, auditable, and unified gateway that transforms raw, messy email data into trusted, context-aware intelligence. Designed for forward-thinking enterprises, it serves as the foundational layer for agentic systems, enabling them to access, comprehend, and act upon information locked within email exchanges and their associated documents. Its core value proposition lies in simplifying the immense technical challenge of email context engineering, offering a single API call that replaces the need for manual parsing, chunking, indexing, and complex prompt tuning. This empowers organizations across sales, customer success, recruiting, and compliance to deploy sophisticated AI assistants and automation with confidence, enhancing productivity, streamlining operations, and maintaining stringent standards of privacy and data governance.
About Threat Watch
In the contemporary digital ecosystem, where cyber threats evolve with alarming sophistication and frequency, maintaining robust security is a universal imperative for every organization. Threat Watch stands as a definitive answer to this challenge, offering a unified cybersecurity intelligence platform that provides unparalleled visibility into an organization's external security posture. It is engineered to function as a continuous diagnostic and monitoring system, meticulously scanning and analyzing an organization's digital footprint across the internet, dark web, and various breach repositories. By aggregating and correlating data from diverse and critical sources—including compromised credentials, exposed assets, phishing campaigns, and dark web chatter—it synthesizes a clear, actionable, and real-time overview of cyber health. This solution is designed for IT security teams, risk management professionals, and executive leaders who seek to transition from a reactive, incident-driven approach to a proactive, intelligence-led security strategy. The core value proposition of Threat Watch is its powerful ability to distill vast oceans of complex threat data into prioritized, comprehensible insights. It automates critical external assessments, enabling organizations to swiftly uncover lurking threats, understand their actual business risk, and orchestrate efficient remediation efforts, thereby significantly reducing the window of exposure and potential operational or reputational damage.
Frequently Asked Questions
iGPT FAQ
How does iGPT ensure the security and privacy of our email data?
iGPT is architected with enterprise-grade security as a core principle. It adheres to a strict zero data training policy, so your data is never used to train or improve any AI models. All processing is done with OAuth-enforced Role-Based Access Control, and the system operates on a zero data retention model—inputs, prompts, and outputs are processed in memory and never stored. Full audit trails ensure all activity is traceable and compliant.
What makes iGPT different from building our own email parsing and retrieval system?
Building a robust, in-house email intelligence system requires significant investment in parsing complex MIME structures, chunking text, managing vector databases, continuously tuning retrieval algorithms, and engineering prompts for context. iGPT abstracts all this complexity away. It provides a single, unified API that handles real-time ingestion, hybrid retrieval, thread reconstruction, and automatic context shaping, allowing your team to focus on building agent logic rather than maintaining fragile data pipelines.
Can iGPT process attachments, and what file types are supported?
Yes, deep attachment processing is a fundamental capability. iGPT automatically extracts text, data, and structural information from a wide variety of documents attached to emails. This includes common formats such as PDFs, Word documents, Excel spreadsheets, PowerPoint presentations, and plain text files, integrating their content seamlessly into the contextual understanding of the email thread.
How quickly can we integrate iGPT and start getting results?
Integration is designed to be immediate and straightforward. iGPT provides a comprehensive SDK, a live playground for testing API requests and responses in real-time, and support for popular frameworks like LangChain. You can connect your email data sources, and with a single API call, begin receiving contextual answers, often seeing first results in a matter of minutes, not weeks.
Threat Watch FAQ
How does Threat Watch discover my organization's digital assets?
Threat Watch employs a combination of advanced discovery techniques, including passive DNS analysis, SSL certificate scanning, and active reconnaissance within safe and legal boundaries. It continuously crawls the public internet and associated data sources to identify all digital properties—such as domains, subdomains, IP addresses, and cloud instances—associated with your organization's brand and infrastructure.
What types of data sources does the platform monitor?
The platform aggregates intelligence from a vast and diverse array of sources. This includes public breach databases, dark web forums and marketplaces, phishing feeds, paste sites, code repositories, SSL certificate logs, and global domain registration data. This multi-source approach ensures comprehensive coverage and reduces the chance of missing critical threat indicators.
Is the free scan truly free, and what does it include?
Yes, the initial scan offered by Threat Watch is completely free and requires no credit card. It provides a snapshot assessment of your organization's security across key categories like exposed credentials, compromised devices, and phishing risks. This serves as a valuable proof-of-concept to demonstrate the platform's immediate value and the specific risks facing your organization.
How does Threat Watch help prioritize which threats to address first?
Threat Watch does not just list findings; it analyzes them through a risk-based lens. Each identified vulnerability or exposure is assigned a dynamic risk score based on factors like exploitability, asset criticality, and active threat context. This scoring system, presented through an intuitive dashboard, clearly highlights the most severe and imminent risks, enabling security teams to focus their efforts where they will have the greatest impact.
Alternatives
iGPT Alternatives
iGPT is a specialized business intelligence platform that transforms enterprise email data into actionable, context-aware insights. It serves as a secure API for integrating AI-driven analysis directly into sales, customer success, and compliance workflows, enabling smarter agentic systems and more efficient operations. Users often explore alternatives for a variety of strategic reasons. These can include specific budget constraints, the need for different feature sets beyond email intelligence, or requirements for integration with a broader or different set of existing platforms and data sources within their tech stack. The search for a different solution is a natural part of finding the optimal fit for an organization's unique operational landscape. When evaluating potential solutions, key considerations should include the depth and security of data handling, the flexibility and power of the API for custom integrations, and the system's ability to provide transparent, auditable insights. The ideal platform will not only offer robust intelligence but will also align with stringent compliance standards and adapt seamlessly to evolving business processes.
Threat Watch Alternatives
Threat Watch is a unified cybersecurity intelligence platform, operating within the business intelligence and security analytics category. It delivers a comprehensive, real-time evaluation of an organization's external digital health by aggregating data from diverse sources like the dark web and breach databases, transforming it into prioritized, actionable insights for proactive defense. Users often explore alternatives for various practical reasons. These can include budget constraints and specific pricing models, the need for integration with an existing security stack, or a requirement for different feature sets tailored to unique organizational workflows. The search for a different solution is a natural part of finding the optimal fit for a company's size, maturity, and specific risk profile. When evaluating any alternative, key considerations should include the depth and real-time nature of threat intelligence coverage, the clarity and actionability of the presented insights, and the platform's ability to automate monitoring to reduce manual overhead. The ideal solution should not just collect data, but effectively contextualize it to empower strategic, risk-based decision-making across technical and business teams.
