Opal44 vs Threat Watch
Side-by-side comparison to help you choose the right tool.
Opal44 delivers AI-driven insights from your website traffic in clear, simple language, making analytics easy to.
Last updated: March 4, 2026
Threat Watch
Threat Watch instantly evaluates your organization's complete cybersecurity health across all critical categories.
Last updated: March 1, 2026
Visual Comparison
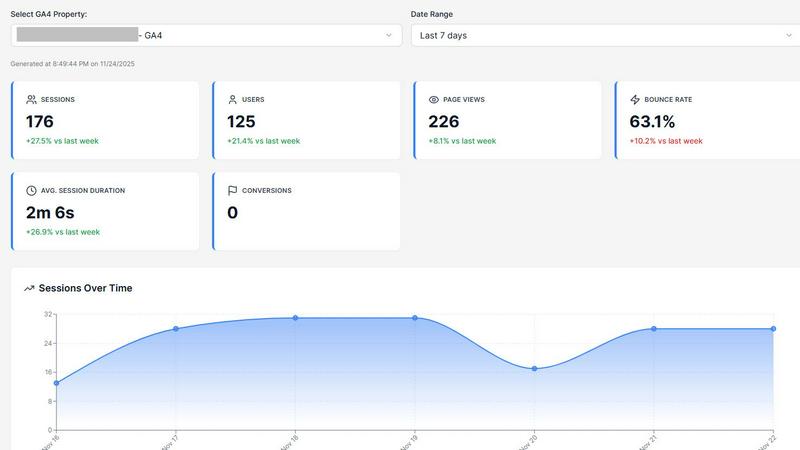
Opal44
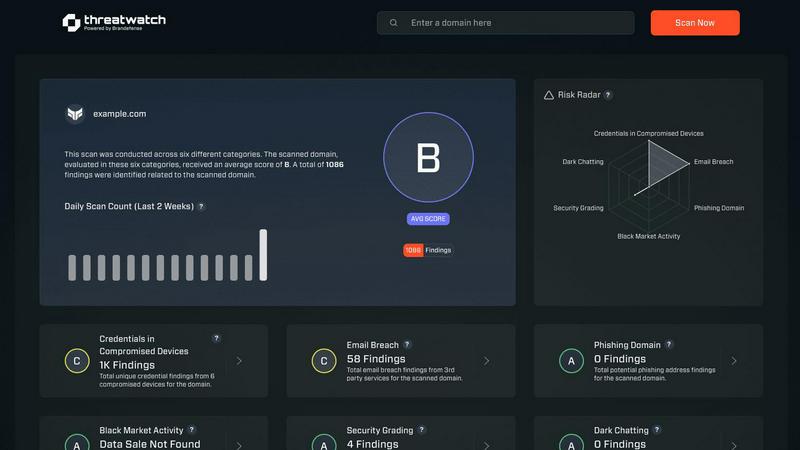
Threat Watch
Feature Comparison
Opal44
Plain English Insights
Opal44 provides clear and concise explanations of your GA4 data in everyday language. This feature eliminates confusion, allowing users to grasp the significance of their website traffic metrics without needing a technical background.
Conversation-Style Reports
The reporting feature of Opal44 reads like a dialogue with a personal analytics guide. This conversational style makes it easy for users to follow along and understand their data, making complex reports accessible to everyone.
Smart, Data-Driven Tips
With Opal44, users receive personalized recommendations based on their GA4 data. These actionable tips are designed to enhance website traffic, improve conversion rates, and facilitate smarter business decisions, ultimately boosting overall performance.
Real-Time Alerts
Stay updated with real-time alerts that notify users of significant changes in website traffic, such as spikes or drops. This feature ensures that you are always informed about your data, allowing for timely responses to unusual activity.
Threat Watch
Comprehensive Digital Footprint Analysis
Threat Watch performs a deep and continuous scan of an organization's external digital presence, identifying all internet-facing assets, domains, and associated infrastructure. This foundational feature maps the entire attack surface, ensuring no blind spots are left unmonitored, which is critical for understanding the scope of potential vulnerabilities and exposures that could be targeted by malicious actors.
Dark Web & Breach Intelligence Monitoring
The platform actively surveils the dark web, underground forums, and a vast array of breach databases to detect if corporate credentials, sensitive data, or intellectual property are being traded or discussed. This proactive monitoring provides early warning signs of compromise long before traditional security tools might alert, allowing for preemptive action such as credential resets and security policy enforcement.
Real-Time Phishing & Impersonation Detection
Threat Watch continuously scans for phishing campaigns, fraudulent domains, and brand impersonation attempts that target the organization and its employees. By identifying malicious sites and email addresses that mimic legitimate ones, it helps prevent successful social engineering attacks and protects the organization's brand integrity and stakeholder trust.
Prioritized Risk Scoring & Actionable Insights
Beyond mere data aggregation, Threat Watch employs advanced correlation and analytics to assign contextual risk scores to every discovered threat and vulnerability. This prioritization transforms raw data into a clear, actionable roadmap for security teams, directing remediation efforts to the issues that pose the most significant business risk first, thereby optimizing resource allocation and response efficiency.
Use Cases
Opal44
Small Business Growth
Small business owners can utilize Opal44 to monitor their website traffic and gain insights into customer behavior. Understanding this data helps them refine marketing strategies and enhance customer engagement.
E-commerce Optimization
E-commerce managers can leverage Opal44's AI-driven recommendations to improve conversion rates. By interpreting analytics in plain English, they can make data-informed decisions that lead to increased sales and profitability.
Digital Agency Reporting
Digital agencies can utilize Opal44 to present analytics to clients in a clear, understandable format. This tool fosters productive strategy meetings by making complex data accessible, ultimately enhancing client relationships.
Content Strategy Development
Content creators can use Opal44 to understand which content resonates most with their audience. By analyzing traffic patterns and user engagement, they can tailor their content strategies to drive higher engagement and reach.
Threat Watch
Proactive External Risk Management
Security and risk management teams utilize Threat Watch to gain a continuous, outside-in view of their organization's security posture. This enables them to identify and assess external threats—like exposed databases, misconfigured cloud storage, or leaked credentials—before they are exploited, allowing for proactive mitigation and strengthening of the overall security framework.
Accelerated Incident Response & Investigation
During a suspected breach or security incident, Threat Watch serves as a critical intelligence source. Teams can quickly investigate if corporate assets or employee credentials have appeared in recent breach dumps or dark web markets, providing crucial context for the incident's scope and origin, which dramatically speeds up containment and eradication efforts.
Third-Party & Supply Chain Risk Assessment
Organizations can extend the platform's monitoring capabilities to assess the cybersecurity health of key vendors, partners, and suppliers. By understanding the external risks present in their supply chain, businesses can make more informed partnership decisions and enforce stronger security requirements, reducing third-party risk exposure.
Executive & Board-Level Security Reporting
Threat Watch provides clear, non-technical dashboards and reports that translate complex threat data into business-centric metrics. This empowers CISOs, executives, and board members to understand the organization's cyber risk in financial and operational terms, facilitating better-informed strategic decisions and cybersecurity investment justifications.
Overview
About Opal44
Opal44 is an innovative analytics tool designed to demystify website traffic data from Google Analytics 4 (GA4). It empowers users—whether small business owners, marketing teams, or content creators—to gain actionable insights without the complexity often associated with traditional analytics platforms. By utilizing advanced AI technology, Opal44 translates intricate data into simple, jargon-free language, allowing users to comprehend their website's performance intuitively. This unique approach not only enhances understanding but also drives informed decision-making. With features such as real-time alerts, tailored recommendations, and a conversational reporting style, Opal44 is ideal for anyone seeking clarity in their analytics, ensuring that the insights generated lead to tangible business growth.
About Threat Watch
In the contemporary digital ecosystem, where cyber threats evolve with alarming sophistication and frequency, maintaining robust security is a universal imperative for every organization. Threat Watch stands as a definitive answer to this challenge, offering a unified cybersecurity intelligence platform that provides unparalleled visibility into an organization's external security posture. It is engineered to function as a continuous diagnostic and monitoring system, meticulously scanning and analyzing an organization's digital footprint across the internet, dark web, and various breach repositories. By aggregating and correlating data from diverse and critical sources—including compromised credentials, exposed assets, phishing campaigns, and dark web chatter—it synthesizes a clear, actionable, and real-time overview of cyber health. This solution is designed for IT security teams, risk management professionals, and executive leaders who seek to transition from a reactive, incident-driven approach to a proactive, intelligence-led security strategy. The core value proposition of Threat Watch is its powerful ability to distill vast oceans of complex threat data into prioritized, comprehensible insights. It automates critical external assessments, enabling organizations to swiftly uncover lurking threats, understand their actual business risk, and orchestrate efficient remediation efforts, thereby significantly reducing the window of exposure and potential operational or reputational damage.
Frequently Asked Questions
Opal44 FAQ
How does Opal44 connect to my Google Analytics account?
Opal44 connects securely to your GA4 account without requiring any code. The setup process is quick and user-friendly, allowing you to start receiving insights in just minutes.
Is my data safe with Opal44?
Yes, Opal44 prioritizes user data security. Your GA4 data remains confidential, as the platform does not sell or share your information with any third parties.
Can I try Opal44 for free?
Absolutely! New users can sign up for a 7-day free trial that includes 50 actions. This allows you to explore all the features without any financial commitment.
What kind of support does Opal44 offer?
Opal44 provides robust customer support, including email assistance and priority support for professional plan users. Help is available 24/7 to ensure you can maximize the value of the platform.
Threat Watch FAQ
How does Threat Watch discover my organization's digital assets?
Threat Watch employs a combination of advanced discovery techniques, including passive DNS analysis, SSL certificate scanning, and active reconnaissance within safe and legal boundaries. It continuously crawls the public internet and associated data sources to identify all digital properties—such as domains, subdomains, IP addresses, and cloud instances—associated with your organization's brand and infrastructure.
What types of data sources does the platform monitor?
The platform aggregates intelligence from a vast and diverse array of sources. This includes public breach databases, dark web forums and marketplaces, phishing feeds, paste sites, code repositories, SSL certificate logs, and global domain registration data. This multi-source approach ensures comprehensive coverage and reduces the chance of missing critical threat indicators.
Is the free scan truly free, and what does it include?
Yes, the initial scan offered by Threat Watch is completely free and requires no credit card. It provides a snapshot assessment of your organization's security across key categories like exposed credentials, compromised devices, and phishing risks. This serves as a valuable proof-of-concept to demonstrate the platform's immediate value and the specific risks facing your organization.
How does Threat Watch help prioritize which threats to address first?
Threat Watch does not just list findings; it analyzes them through a risk-based lens. Each identified vulnerability or exposure is assigned a dynamic risk score based on factors like exploitability, asset criticality, and active threat context. This scoring system, presented through an intuitive dashboard, clearly highlights the most severe and imminent risks, enabling security teams to focus their efforts where they will have the greatest impact.
Alternatives
Opal44 Alternatives
Opal44 is an innovative tool in the realm of business intelligence, designed to provide users with AI-powered insights about their website traffic through Google Analytics 4. By distilling complex data into simple, actionable English, Opal44 enables users to understand their web traffic without the confusion of technical jargon. This accessibility makes it an appealing choice for businesses aiming to enhance their online presence and make informed decisions based on user behavior. However, users often seek alternatives to Opal44 due to various reasons such as pricing considerations, specific feature sets, or compatibility with other platforms. When evaluating an alternative, it is essential to consider factors like ease of use, the comprehensiveness of insights, integration capabilities, and the overall value offered. Choosing the right solution can significantly impact a business's ability to analyze data effectively and drive growth.
Threat Watch Alternatives
Threat Watch is a unified cybersecurity intelligence platform, operating within the business intelligence and security analytics category. It delivers a comprehensive, real-time evaluation of an organization's external digital health by aggregating data from diverse sources like the dark web and breach databases, transforming it into prioritized, actionable insights for proactive defense. Users often explore alternatives for various practical reasons. These can include budget constraints and specific pricing models, the need for integration with an existing security stack, or a requirement for different feature sets tailored to unique organizational workflows. The search for a different solution is a natural part of finding the optimal fit for a company's size, maturity, and specific risk profile. When evaluating any alternative, key considerations should include the depth and real-time nature of threat intelligence coverage, the clarity and actionability of the presented insights, and the platform's ability to automate monitoring to reduce manual overhead. The ideal solution should not just collect data, but effectively contextualize it to empower strategic, risk-based decision-making across technical and business teams.
